Move over '123456': passwords to go high-tech
Internet users may soon have a secure solution to the modern plague of passwords, in which they can use visual patterns or even their own body parts to identify themselves.
Developers at the world's biggest high-tech fair, CeBIT, say that one of the biggest frustrations of having a smartphone and a computer is memorising dozens of sufficiently airtight passwords for all their devices and accounts.
"The problem of passwords is that they are very weak, they are always getting hacked, and also from a user point of view, they are too complicated, everybody has 20, 30, 60 passwords," said Steven Hope, managing director of Winfrasoft from Britain, the fair's guest country this year.
"They all have to be different, no one can remember them, so everybody writes them down or resets them every time they log in. They don't work in the real world today."
Passwords have proliferated so much that it's a daily struggle for users to cope with so many of them.
And as millions of Internet users have learned the hard way, no password is safe when hackers can net them en masse from banks, email services, retailers or social media websites that fail to fully protect their servers.
Many simply throw in the towel and use no-brainer codes like "123456" and "password"—which are still the most common despite how easily they can be cracked, CeBIT spokesman Hartwig von Sass said at the event in the northern German city of Hanover.
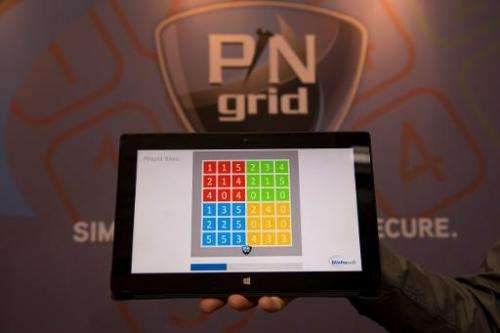
In response to the vulnerabilities and hassles of the antiquated username-and-password formula, Winfrasoft has developed an alternative based on a four-colour grid with numbers inside that resembles a Sudoku puzzle.
Users select a pattern on the grid as their "password" and because the numbers inside the boxes change once per minute, the code changes too, making it far harder to hack.
"There is no way anybody could see which numbers you are looking at. You see typing numbers but you don't know what the pattern is because each number is here six times," Hope said during a demonstration.
Backup from body parts
Biometric data offers another alternative to seas of numbers, letters and symbols.
US giant Apple has already equipped its latest generation iPhone with a fingerprint reader to boost its security profile.
But a group of European hackers, the Hamburg-based Chaos Computer Club, demonstrated that the system could be pirated using a sophisticated "fake" fingerprint made of latex.
Japan's Fujitsu turned to the other end of the hand and has developed an identification system based on each person's unique vein pattern.

At its CeBIT stand, the company was showing off its PalmSecure technology on its new ultra-light laptop computer which has a small sensor built in.
Meanwhile Swiss firm KeyLemon has developed a face recognition system using a webcam.
The computer registers parts of the face, "the eyes, the eyebrows, the shape of your nose, your cheekbones, the chin..." a company spokesman said.
The person must then only sit in front of the screen to be recognised and gain access to the computer.
The system, already used by some three million people according to the company, still has a few kinks however so users must remember to take off their eyeglasses, for example, or have consistent lighting in order to pass the identity test.
"Face recognition and fingerprint recognition are additional safety security features, they will never have only face recognition or fingerprint recognition" but rather use them as a crucial backup to passwords, he said.
© 2014 AFP

















