June 13, 2006 feature
Scientists develop algorithm for ultra-secret security technique
To achieve a high capacity security system that is exceedingly robust to attacks, scientists have developed a set of instructions to unlock secret information, avoiding the need for embedding images and the risks involved.
Information theft has become one of the most feared types of theft due to the vast power that comes with possessing certain information. Our numbers – social security numbers, credit card numbers, passwords, bank accounts, etc. – give authorization to access private documents and assets, and attempts to hack such accounts are ongoing.
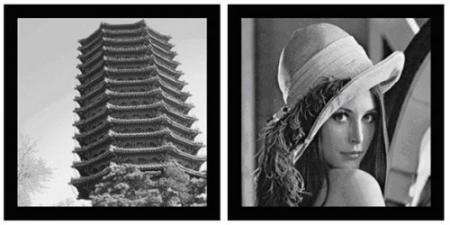
Optical security, which consists of hiding a secret image and includes methods such as holography and virtual optics, has been a growing field in security over the last few years. Until now, optical techniques have required the embedment of a secret image in a host image. Although a logical hiding procedure, embedded images can often be found in watermarked images, jeopardizing the security of the system. (Watermarks are the visible but difficult-to-replicate marks used to protect against fraud, while the host image is the visible, normally printed image covering the secret information.)
To address this problem of finding the secret image in the watermark, scientists have developed a new optical security method that doesn’t require embedment. Instead, the technique uses a phase retrieval algorithm to generate specific optical and phase keys that extract the secret information when applied. The optical keys contain information and are distributed to an individual through a personal identification number (PIN). The information contained in the phase keys (the main source for determining extraction) is distributed to the individual separately.
“The phase keys, designed by the phase retrieval algorithm, modulate the amplitude of the input [host] image into the amplitude of the secret image by the two Fresnel transformations,” Yishi Shi, coauthor of the paper in a recent issue of Journal of Optics A, told PhysOrg.com. “The phase keys are the main keys for the extraction of the secret image. The second type of key, the additional optical keys (which include the wavelength key and the mask position key) are also employed in our Fresnel system, which help to achieve a higher security level than can be achieved by Fourier systems.”
This technique, which the scientists call “optical Fresnel image hiding (OFIH)”, satisfies “the three most important requirements in image hiding,” according to the team. Because no embedding occurs – meaning that the secret image cannot be found in the watermarked image – the method satisfies the so-called “imperceptibility requirement.” Since the watermarked image contains no secret information, and the phase keys are the main method for extraction, the OFIH method also satisfies the “robustness requirement.” Finally, since the secret image is the same size as the host image, this method also satisfies the “capacity requirement.”
Another advantage of this optical technique is that one host image can hide several different secret images. In addition, one secret image can be hidden in different host images. These multiple variations further enhance the flexibility and robustness of the system.
“This system is designed as a fragile system that may be used for authentication, and also could be designed as a robust or semi-fragile system for the purpose of image hiding or digital watermarking,” said Shi. “If we adopt the pure digital method to apply the Fresnel system, its realization will much easier. Thus, the flexibility of the designs for different application purposes is also obtained in the OFIH, allowing us to implement the system either by pure digital method or the opt-digital method.”
Citation: Shi, Yishi, Situ, Guohai and Zhang, Jingjuan. Optical image hiding in the Fresnel domain. Journal of Optics A: Pure and Applied Optics. 8 (2006) 569-577.
By Lisa Zyga, Copyright 2006 PhysOrg.com. All rights reserved. This material may not be published, broadcast, rewritten or redistributed.




















