Color sudoku puzzle demonstrates new vision for computing
Researchers at the University of Warwick’s Department of Computer Science have developed a colour based Sudoku Puzzle that will help Sudoku players solve traditional Sudoku puzzles but also helps demonstrate the potential benefits of a radical new vision for computing.
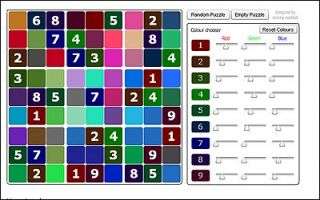
The colour Sudoku adds another dimension to solving the puzzle by assigning a colour to each digit. Squares containing a digit are coloured according to the digit's colour. Empty squares are coloured according to which digits are possible for that square taking account of all current entries in the square's row, column and region. The empty square's colour is the combination of the colours assigned to each possible digit. This gives players major clues as darker coloured empty squares imply fewer number possibilities.
More usefully an empty square that has the same colour as a completed square must contain the same digit. If a black square is encountered then a mistake has been made. Players also can gain additional clues by changing the colour assigned to the each digit and watching the unfolding changes in the pattern of colours.
Sudoku players can test this for themselves at: www.warwick.ac.uk/go/sudoku. (NB page requires Flash 9)
However the colour Sudoku is more than just a game to the University of Warwick Computer Scientists. For doctoral researcher Antony Harfield it is a way of exploring how logic and perception interact using a radical approach to computing called Empirical Modelling. The method can be applied to other creative problems and he is exploring how this experimental modelling technique can be used in educational technology and learning.
The interplay between logic and perception, as it relates to interactions between computers and humans is viewed as key to the building of better software. It is of particular relevance for artificial intelligence, computer graphics, and educational technology. The interaction between the shifting colour squares and the logical deductions of the Sudoku puzzle solver is a good illustration of the unusual quality of this "Empirical Modelling" approach.
Previously the researchers have been able to use their principles to analyse a railway accident in the Clayton Tunnel near Brighton when the telegraph was introduced in 1861. Reports at the time sought to blame various railway personnel but by applying Empirical Modelling the researchers have created an environment in which experimenters can replay the roles of the drivers, signalmen and other personnel involved. This has shown that there were systemic problems arising from the introduction of the new technology.
Dr Steve Russ of the Empirical Modelling group at the University of Warwick said:
"Traditional computer programs are best-suited for tasks that are so well-understood they can, without much loss, be expressed in a closed, mechanical form in which all interactions or changes are ‘pre-planned’. Even in something so simple as a Sudoku puzzle humans use a mixture of perception, expectation, experience and logic that is just incompatible with the way a computer program would typically solve the puzzle. For safety-critical systems (such as railway management) it is literally a matter of life and death that we learn to use computers in ways that integrate smoothly with human perception, communication and action. This is our goal with Empirical Modelling."
Source: University of Warwick





















