US conducted 231 'offensive cyberoperations': report
US spy services conducted 231 "offensive cyberoperations" in 2011, mostly targeting Iran, Russia, China and North Korea, the Washington Post reported on Saturday.
The revelation is based on a classified intelligence budget provided to the paper by fugitive leaker Edward Snowden, as well as on interviews with former US officials.
The Post also reported that, under a $652 million project code-named "GENIE," US specialists hack foreign computer networks to secretly put them under American control.
This involves placing "covert implants" in computers, routers and firewalls, it said, adding that by year's end "GENIE" is projected to control at least 85,000 "malware" plug-ins in machines around the globe.
That compares to just over 21,200 in 2008, the Post reported, citing the intelligence budget.
"The documents provided by Snowden and interviews with US officials describe a campaign of computer intrusions that is far broader and more aggressive than previously understood," the daily said.
Of the 231 "offensive operations" conducted in 2011, nearly 75 percent were against top-priority targets that the Post, citing former officials, said included "adversaries such as Iran, Russia, China and North Korea and activities such as nuclear non-proliferation."
The paper said US intelligence services make "routine use" of government-constructed malware around the globe that "differs little in function from the 'advanced persistent threats' that US officials attribute to China."
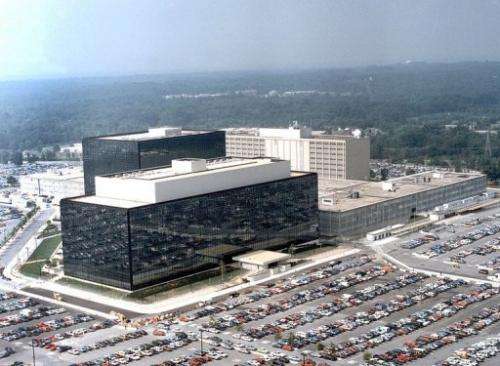
However, while an unnamed National Security Agency spokesman confirmed to the Post that the Defense Department does engage in computer network exploitation, the paper also quoted him as saying that, unlike China, "the department does ***not*** engage in economic espionage in any domain, including cyber."
Snowden, a former US National Security Agency contractor, was granted temporary asylum in Russia on August 1.
He is wanted by Washington on espionage charges linked to media disclosures about US surveillance programs.
© 2013 AFP




















