September 5, 2012 report
Researchers find most BitTorrent users being monitored
(Phys.org)—Researchers from Birmingham University in the UK have found that users who frequent BitTorrent file sharing sites such as The Pirate Bay, risk having their IP address logged by monitors as quickly as within three hours of getting on. The team, led by Tom Chothia, discovered the extent to which monitors are tracking users on such sharing sites by monitoring activity themselves over a two year period. They found as they note in their paper presented this week at the SecureComm conference, that virtually all users of such sites wind up having their IP address noted and recorded at some point.
BitTorrent file sharing sites work by means of a Peer to Peer sharing scheme. Users log in and download chunks of a file they want from several different other users at the same time who share the load as a swarm. At the same time, files that they've already downloaded are shared with others. The protocol and hosting sites, known as trackers don't differentiate between files that are traded legally, or illegally, hence the presence of monitors, which are "users" or clients that log in for the express purpose of finding out who is downloading illegal content. The very nature of the protocol makes it very easy for such monitors to note which users are downloading which files as it's all tracked via IP addresses.
One way to get around having an IP address cataloged by a monitor is to block their IP address; disallowing them from joining the swarm that is sending pieces of files. Users who frequent BitTorrent sites generally become aware of what are known as blocklists (lists of the IP addresses of known monitors); unfortunately, the researchers found such lists to include many false positives and negatives, making them generally useless in preventing monitoring.
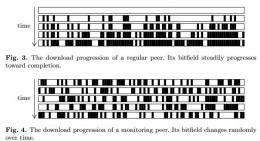
To figure out which clients were real users and which were monitors, the researchers noted several characteristics of the monitors that make them stand out. One was the fact that monitors tend to hold a large number of the subnets that access sharing sites. Other ways were that they tend to stay connected a lot longer than regular clients and to connect to a lot more swarms and also generally fail to report actually ever completing downloads. In short, they are simply much busier and active, though with little to show for it, than users who generally tend to only log on when they want a certain file and then go away for a period of time after they get it.
After compiling lists of IP addresses they suspected of belonging to monitors, the team compared them against other known information about such IP holders and were able to verify that many of them were indeed known BitTorrent monitoring entities. They conclude by making it clear that virtually everyone that uses such sites to download files will have their IP address cataloged at some point, but add that the information gathered by such monitors likely wouldn't withstand legal scrutiny.
More information:
© 2012 Phys.org



















