May 13, 2011 weblog
Security flaws found in the WebGL standard

(PhysOrg.com) -- Researchers at Context Information Security have issued a warning about the WebGL standard. The warning states that this standard has the potential to undermine the security concepts that are practiced by current operating system versions and provide a new set of opportunities for attacks on a variety of system.
The standard, which is designed to enabled the rendering of 3D animations, executes the shader code directly on the system's graphics card. While this may make graphics rendering simpler, it does however make a space for the exploitation. If the graphics card has any vulnerability in it the system could be breached. This level of vulnerability is something that the Khronos Group, who are the creators of the WebGL standard, have acknowledged the possibility of in the WebGL specifications.
How serious are the potential vulnerabilities? Well, the researchers at Context Information Security say that they have been able to create the blue screen of death by using an exploitation that targets the overloading of a graphics card. While some of the current operating systems do have a fail-safe that rests an overloaded graphics card after a few seconds, the blue screen of death can be reached after a certain number of resets.
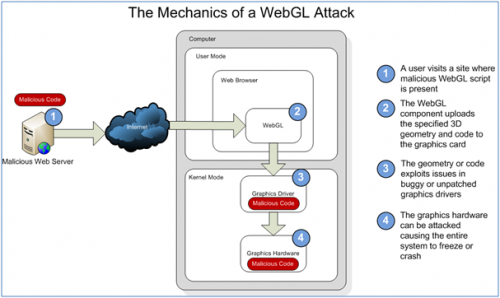
The flaw could also, according to the researchers, be used to not just create the blue screen of death, but to inject malicious code onto the system.
There is no word yet as to whether or not the standard will be changed, or when any changes to the standard would be implemented. Since the problem is already known and published in the standard it may not change at all.
More information: Report: www.contextis.com/resources/blog/webgl/
© 2010 PhysOrg.com

















